### Summary
On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.
### Details
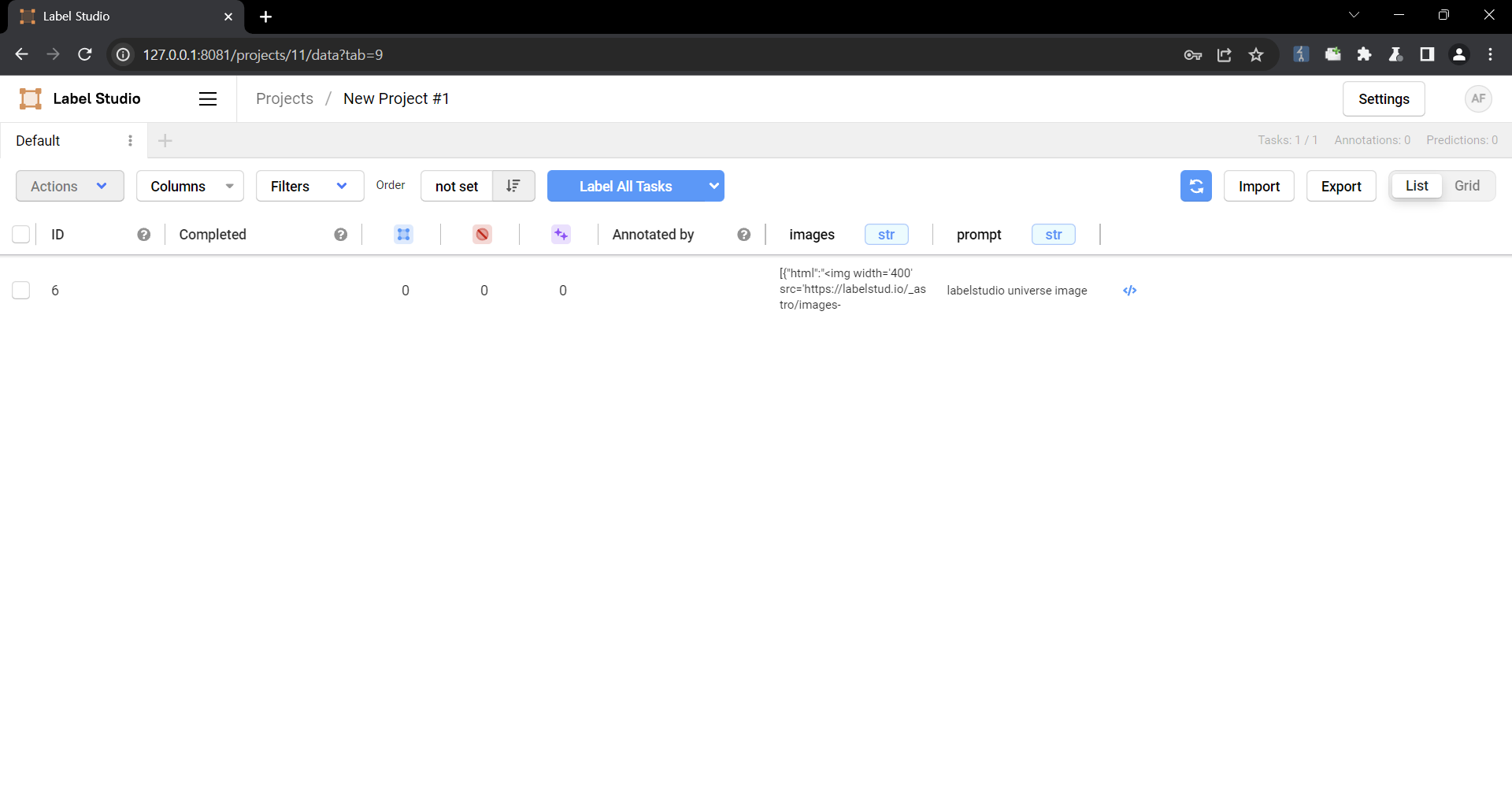
Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1.
### PoC
1. Create a project.

2. Upload a file containing the payload using the "Upload Files" function.


The following are the contents of the files used in the PoC
```
{
"data": {
"prompt": "labelstudio universe image",
"images": [
{
"value": "id123#0",
"style": "margin: 5px",
"html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>"
}
]
}
}
```
3. Select the text-to-image generation labeling template of Ranking and scoring


4. Select a task
5. Check that the script is running
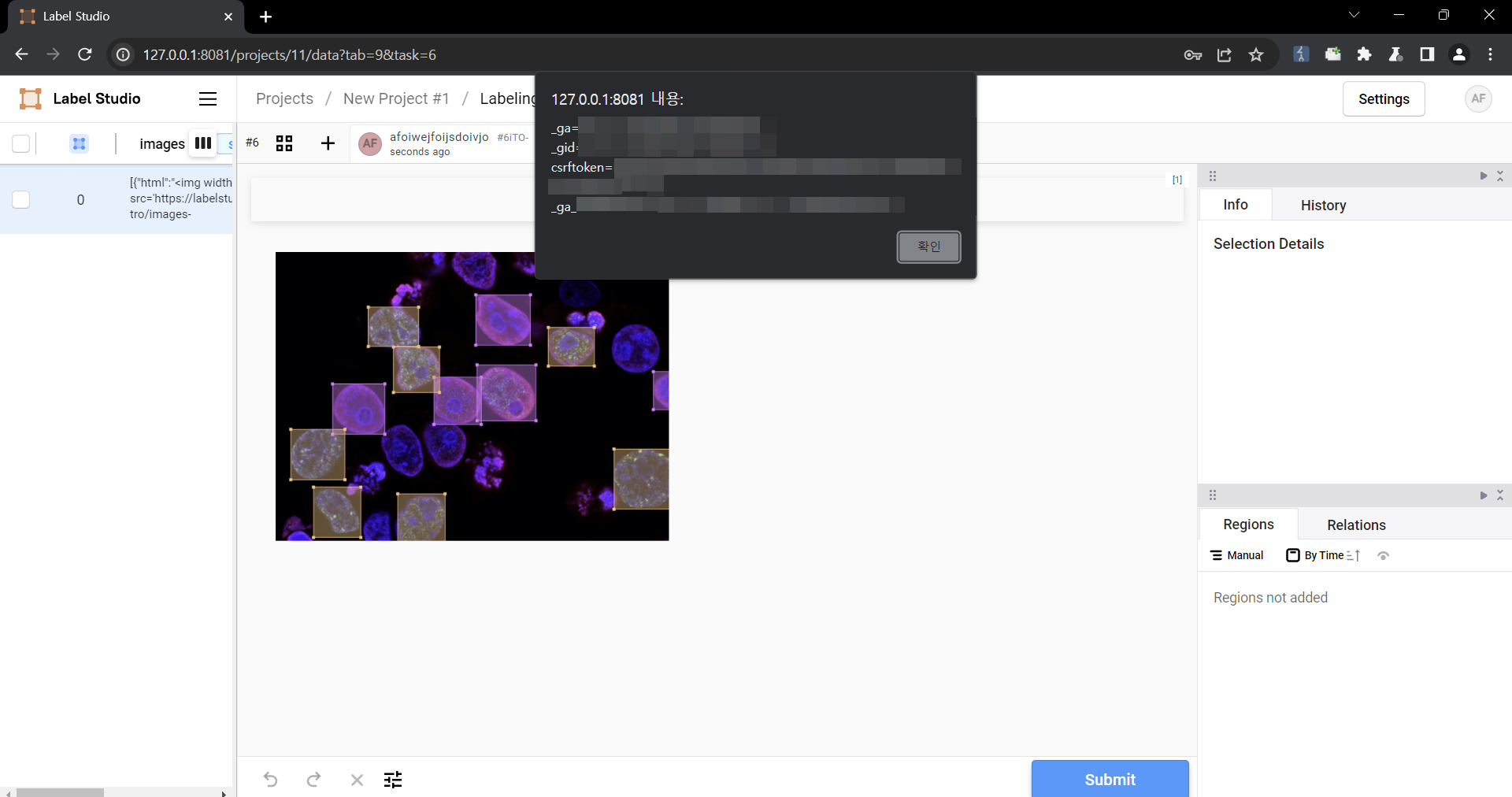
### Impact
Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
Metrics
Affected Vendors & Products
References
History
Sun, 13 Jul 2025 13:45:00 +0000
| Type | Values Removed | Values Added |
|---|---|---|
| Metrics |
epss
|
epss
|
Fri, 16 May 2025 14:45:00 +0000
| Type | Values Removed | Values Added |
|---|---|---|
| First Time appeared |
Humansignal
Humansignal label Studio |
|
| CPEs | cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:* | |
| Vendors & Products |
Humansignal
Humansignal label Studio |
Status: PUBLISHED
Assigner: GitHub_M
Published: 2024-02-22T21:52:26.193Z
Updated: 2024-08-14T15:32:05.054Z
Reserved: 2024-02-14T17:40:03.690Z
Link: CVE-2024-26152
Updated: 2024-08-01T23:59:32.696Z
Status : Analyzed
Published: 2024-02-22T22:15:47.310
Modified: 2025-05-16T14:18:25.530
Link: CVE-2024-26152
No data.
